Video Game Security Bug Bounty Programs

Gaming platforms continue to prove a tempting target for cybercriminals, with the industry’s value estimated at $152 billion worldwide. and now video game developers ask white hats for help. Last year’s Akamai State of the Internet report describes in detail how 12 billion credential stuffing attacks targeted players over a 17-month period. To combat the […]
Continue readingWhat is Ethical Hacking & Pen-Testing?
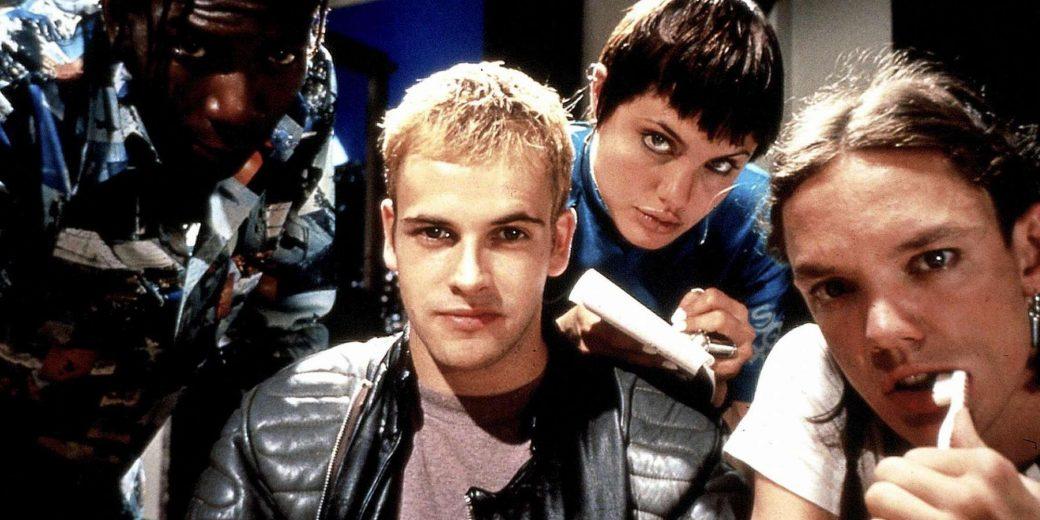
When you hear the word “hacker” you often think of cyber criminals and bad guys with hoodies, or if you’re old enough the movie hackers. However, there is another bread of white hat “good guys” called ethical hackers or penetration testers. But what is ethical hacking? Penetration testing companies use ethical hacking and pen testing […]
Continue readingWhat are Some Security Issues in Cloud Storage?
Nowadays, there are a lot of options when it comes to saving your files and making extra copies for safekeeping. These extra copies can be saved using other storage options besides hardware. Enter the cloud. The cloud is an excellent way to store files you need to back up without having to buy hardware which […]
Continue reading